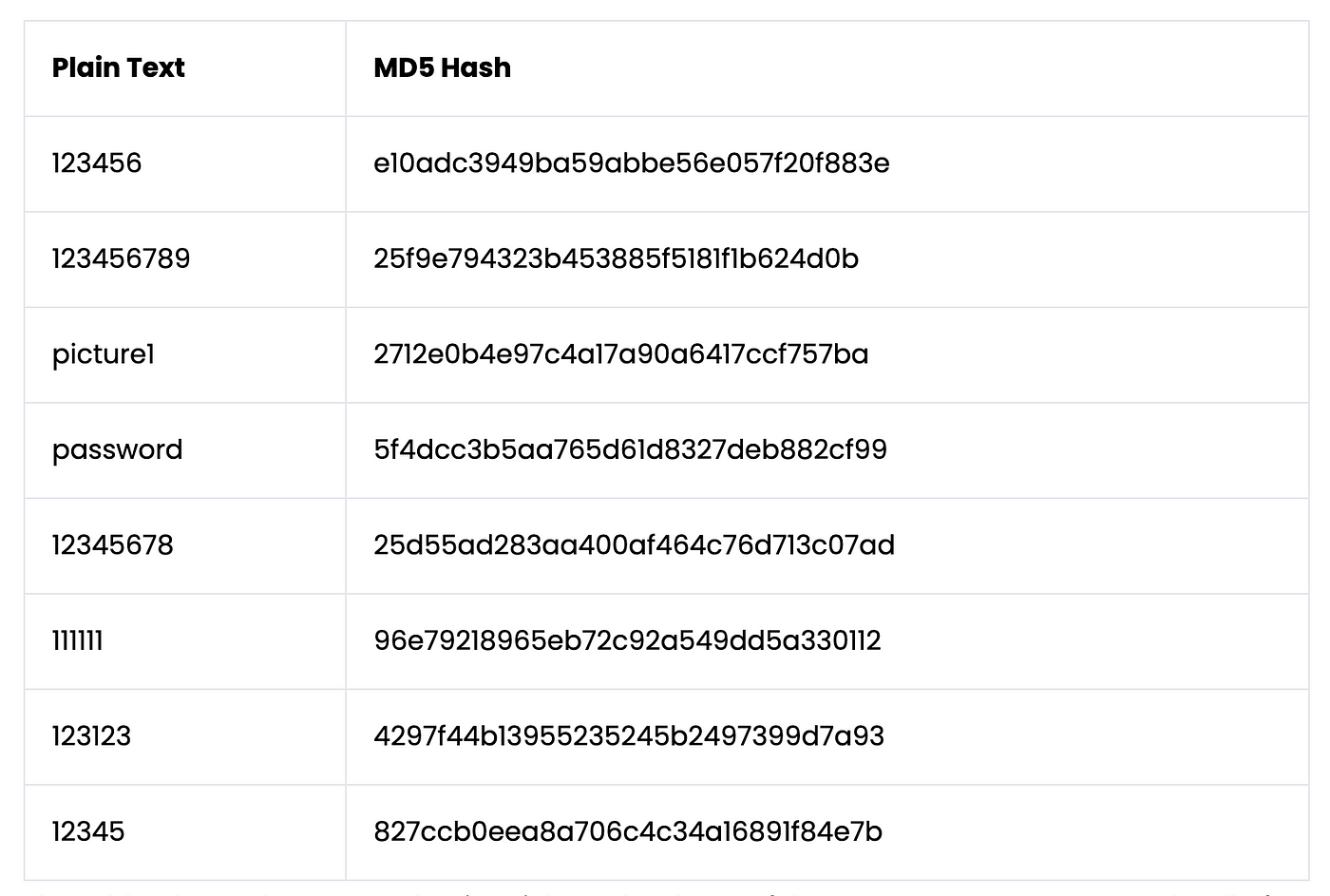
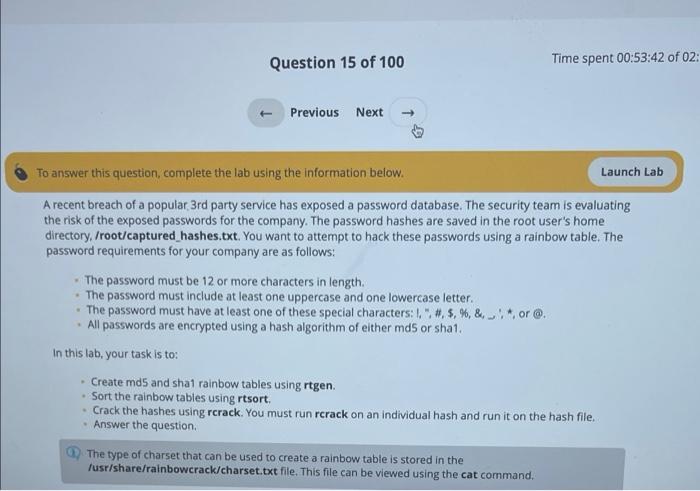
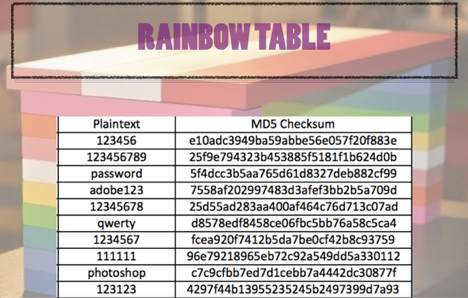
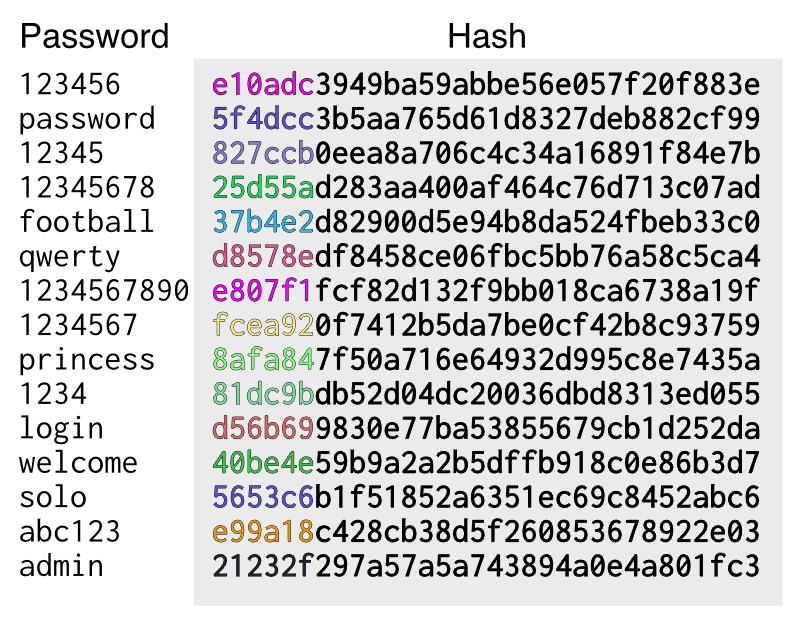
8.3.6 Analyze Passwords using Rainbow Tables - 8.3 Analyze Passwords using Rainbow Tables Determine - Studocu

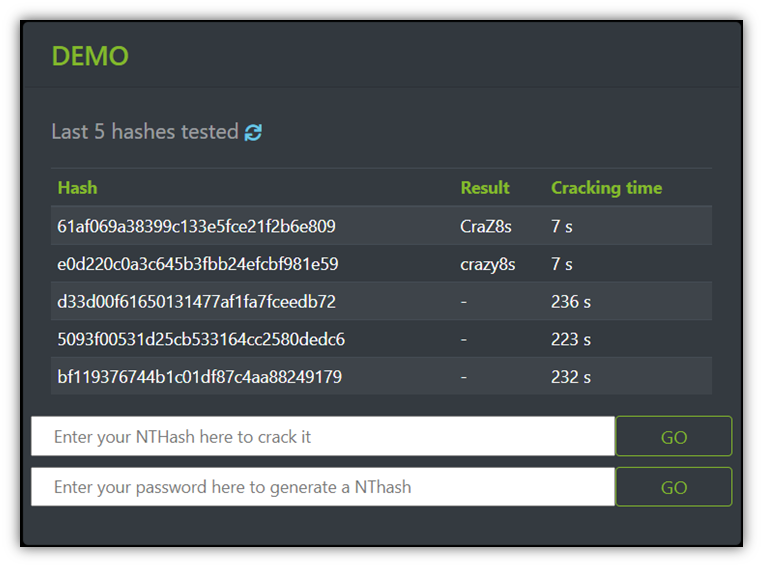
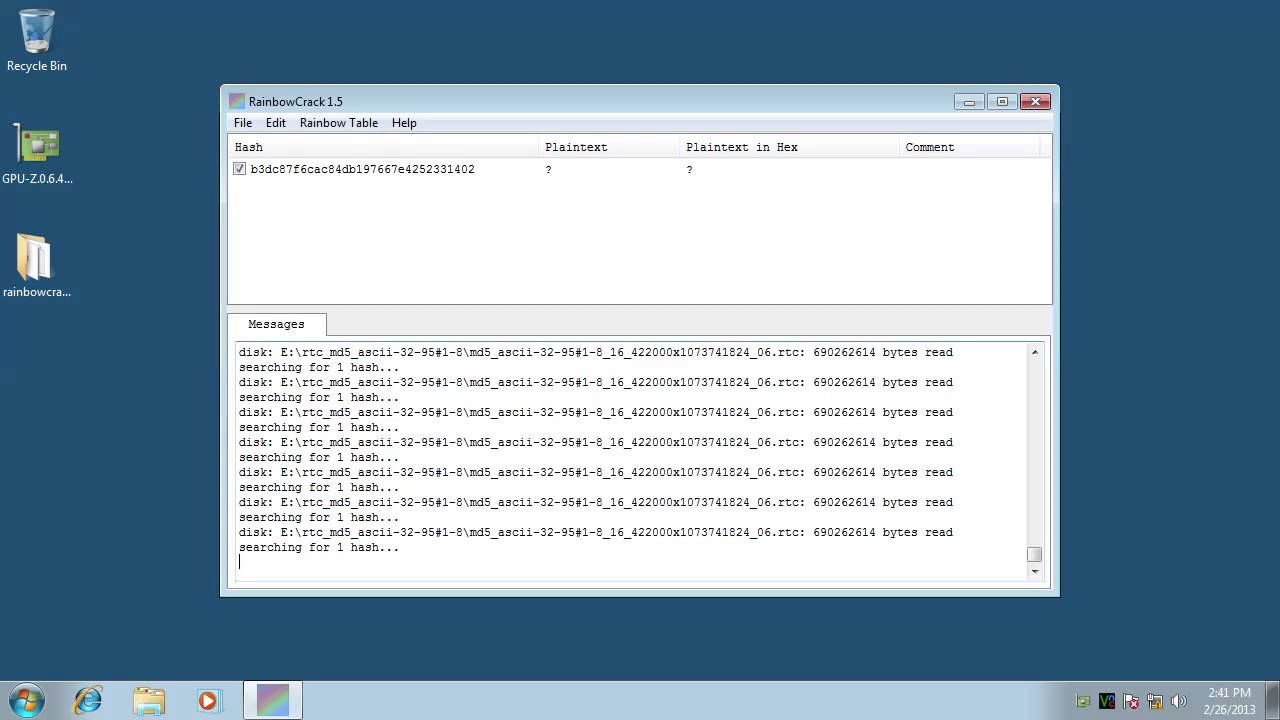
KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022

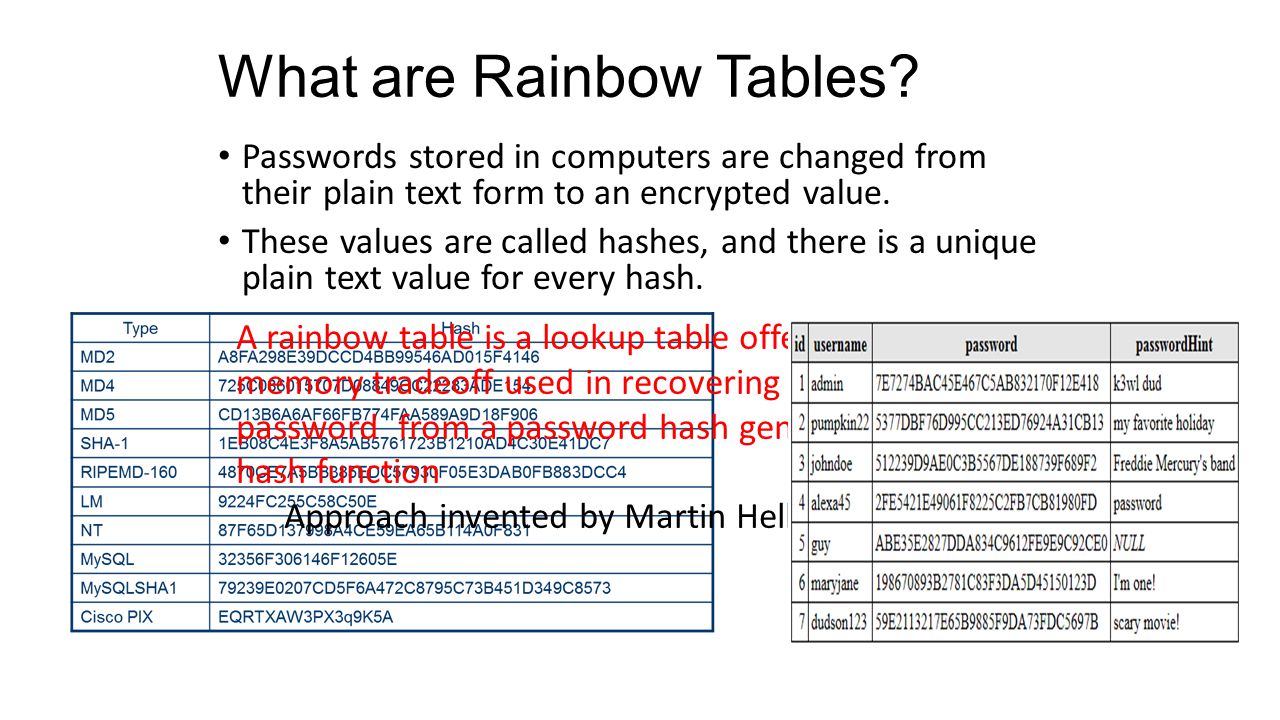
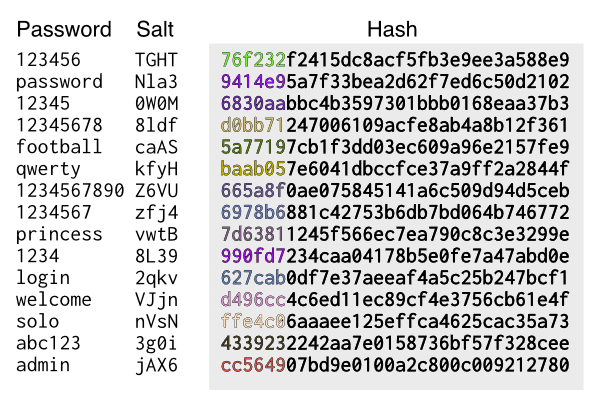
I͛P͛h͛o͛n͛e͛G͛a͛l͛a͛x͛y͛M͛D͛ 10K͛ 🏴☠️ on X: "Rainbow table attack #attack #attacks #cyber #cybersecurity #cyberattack #hash #table #hashing #hac #hacks #hack #hacker #hacked #hacker #hackers #hacking #ddos #awareness #aware #safe #security ...